References
Satisfied customers speak for themselves! Here you will find numerous examples from various industries. We would like to thank our customers for their permission.
- Show all
- E-Mobility
- Environmental & Recycling Technology
- Medical & Pharmaceutical
- Metalworking
- Packaging machines
- Paper & Printing Industry
- Plastics machines
- Robotics
- Shipbuilding
- Test Systems
- Textiles machines
High-precision and powerful with direct drive technology
Working with Baumüller, Bemaco Engineering developed a highly productive plastic blow-molding machine with fully electric clamping unit

Efficiency in Detail
Baumüller equips thermoforming machines with efficient and comprehensive automation systems
- Higher degree of effectiveness with synchronous motors
- Faster and more efficient thanks to software modules
- Intuitive engineering

Servo pump solution for higher efficiency
Hürmak, the Turkish market leader in plastic injection molding machines, has been able to achieve higher energy efficiency, reproducibility, and product stability in its machines thanks to the servo pump solution from its automation partner Baumüller.
- Servo pump solution optimizes hydraulic machine
- Servo pump solution for higher efficiency

Bagged - Fast and Safe
Servo drives from Baumüller ensure increased productivity and a guaranteed manufacturing quality of the packaging in the automatic bottom seam machines from LWKB, e.g. for the food, electrical or packaging industries.

Film bag machine
Baumüller engineering specialists have designed a foil bag machine for Lemo, which allows maximum flexibility and fast commissioning.

Punching machine
What no-one expects: The manufacture of paper cups is highly complicated, precision and dynamics are demanded from the machines. The new Drusula 1200S punching machine from Weyhmüller easily meets requirements with a Baumüller drive and control system.
The magic is in the details
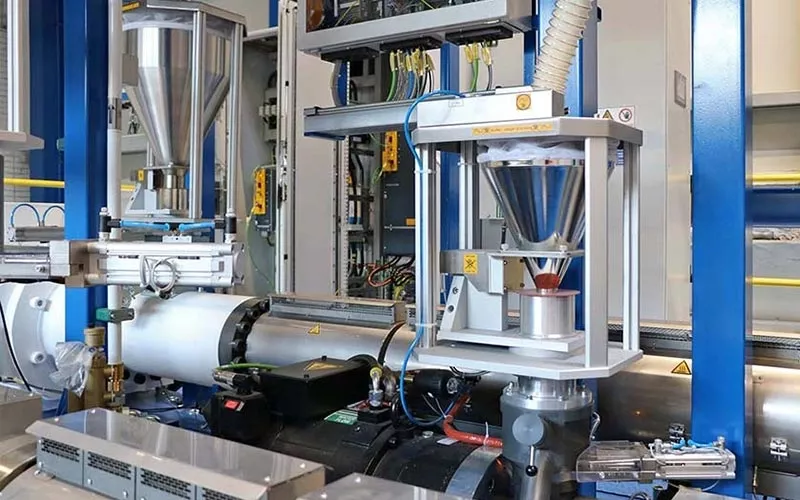
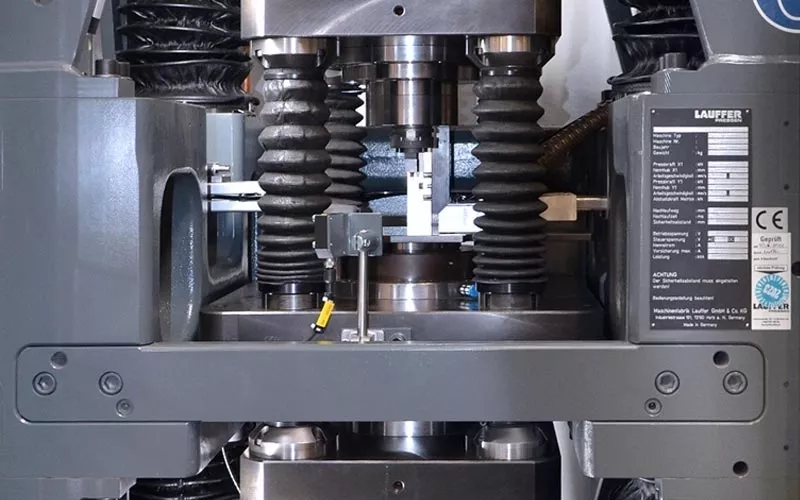
Baumüller supplies a precisely controllable drive system for the newly developed electric powder press from Maschinenfabrik Lauffer.
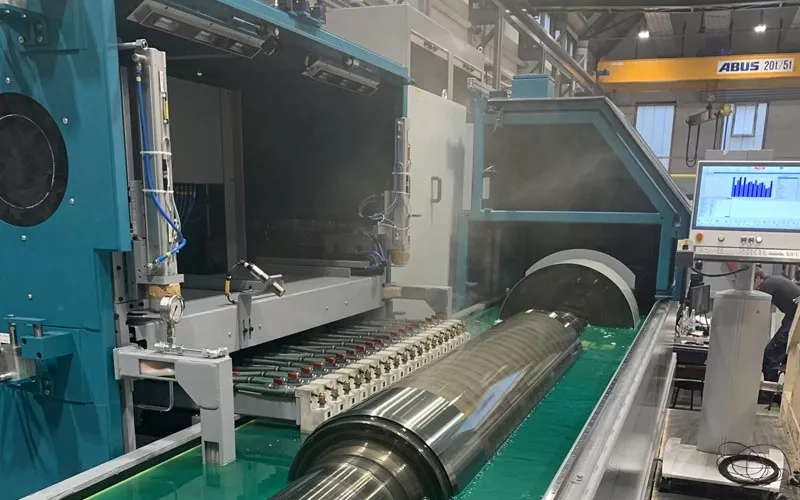
Sparks are flying – precisely and decentrally positioned
The texturing machines from Maschinenfabrik Herkules use electric arcs to process the rolls with the utmost accuracy. Now, the drive specialist Baumüller has assisted in optimizing the machines by converting them to decentralized drive technology.

Complete solution from a single source for highly dynamic servo presses
Baumüller equips the Simpac MX and SX servo press series with highly dynamic drive and automation solutions.

High-precision 3D eye rim bending machine
The latest version of the fully automated 3D eye rim bending machine S-514 from Schüssler Technik is compact, digital, and meets the requirements of Industry 4.0 - and it allows glasses manufacturers around the world to have creative design options.
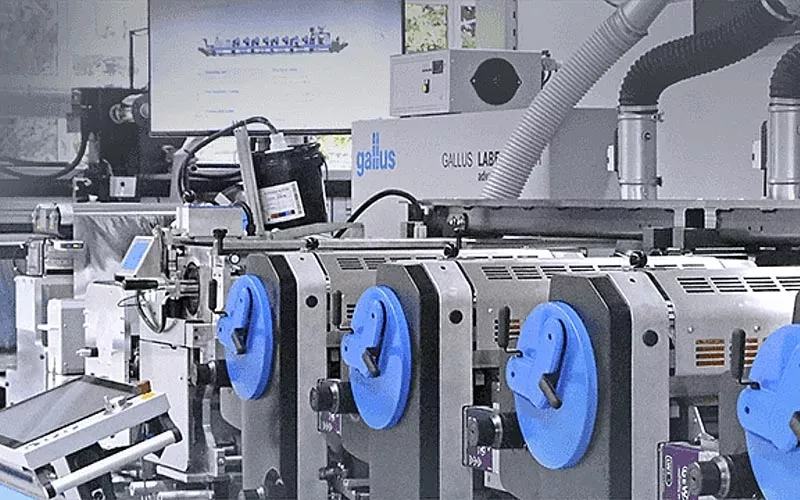
Razor Sharp at High Speed
Baumüller is supporting Gallus in developing a new label printing machine in the field of drive technology. The Gallus Labelmaster exceeds its predecessor models both in terms of speed and in terms of flexibility.

An ingenious solution: From metal wool to metal fiber yarn
In cooperation with Baumüller and the Technical University of Dresden, Deutsche Metallfaserwerk Dr. Schwabbauer GmbH & Co. KG has developed a yarn winder for the production of metal fiber yarn with six drives and an application-optimized software solution

Multi-needle quilting machine comprehensively automated
Dahmen equipped its multi-needle quilting machine with Baumüller drive components. The complete package with a integrated analysis tool ensures maximum productivity.

Multi-needle lock stitch
In cooperation with Baumüller, Dahmen has developed the world's most productive multi-needle lockstitch machine with a 1'' needle gauge

Precision mixed with mobile drive systems
Baumüller is realizing mixing systems for foaming agents together with the fire truck manufacturer Rosenbauer. The pressurized foam mixing system DIGIMATIC42 is electrically driven with a controller and motor from Baumüller.

Baumüller intelligent power management system eliminates the need for redundancy and saves additional fuel
The VSS Emmerich features a diesel-electric propulsion system with an intelligent power management system. Two diesel generators with an output of 294 kW each provide the power for the two electric drive motors, the bow thruster, and the on-board electronics.

Starting signal for an all-electric, emission-free inland waterway transport fleet
The partnership between SNL and Baumüller marks a milestone in the electrification of waterborne transport in Switzerland.

New Hybrid Ferry in Denmark
Drive and automation specialist Baumüller receives order from Danish shipyard Hvide Sande to supply a hybrid drive system

Hybrid ferry with Baumüller drive system
Environmentally Friendly Across the Weser River - Four Baumüller electric motors drive the drive propellers of the ferry Farge directly.

Hybrid marine power from Baumüller
Economical, environmentally and equipped throughout with the latest technology, the new coastal work boat Trischen is evidence that alternative marine propulsion solutions have long since come on board.

First Electric Ferry in Asia
The first fully electric passenger ferry in Asia is operating with Baumüller technology and uses solar power

Energy consumption reduced by 15 percent
Baumüller supplied an energy-efficient direct drive for a newly developed tablet press from Fette Compacting. (Title photo: Fette Compacting)

Compact and powerful stair lift motors
Flat, light, powerful, and dynamic – Baumüller supplies disc motors of the type GDM 10 N as a main drive for stair lifts. The compact drive package offers the possibility of designing the entire lift in a minimum size.

The circular economy meets energy efficiency: 30 percent lower energy costs thanks to direct drive technology
Working with Baumüller, WEIMA Maschinenbau GmbH developed a high throughput single shaft crusher with high-torque drive

Welding robot
In the joint project of Cloos and Baumüller, the six-axis articulated welding robot QIROX QRH-280, the best of two industries were linked with each other
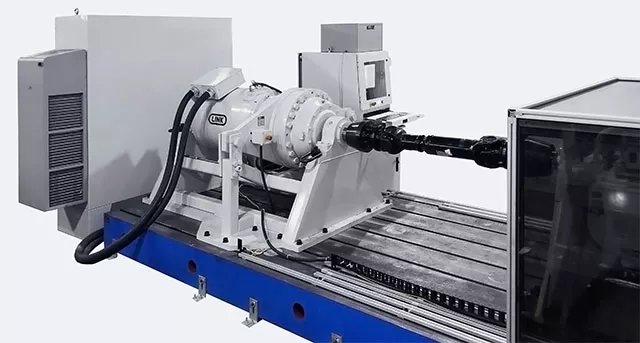
Testing platform with high-torque technology
The combination of the LINK 3500 Test Controller and Baumueller b maXX servo drive leveraged each of the products strengths and features to produce a powerful but easy to use testing platform.



